-

Using Platform Hub to increase Supply Chain Security
-

Focus on your end users when creating AI workloads
-

Lessons from Crowdstrike's outage
-
Feature branch environments with Kubernetes and Octopus
-
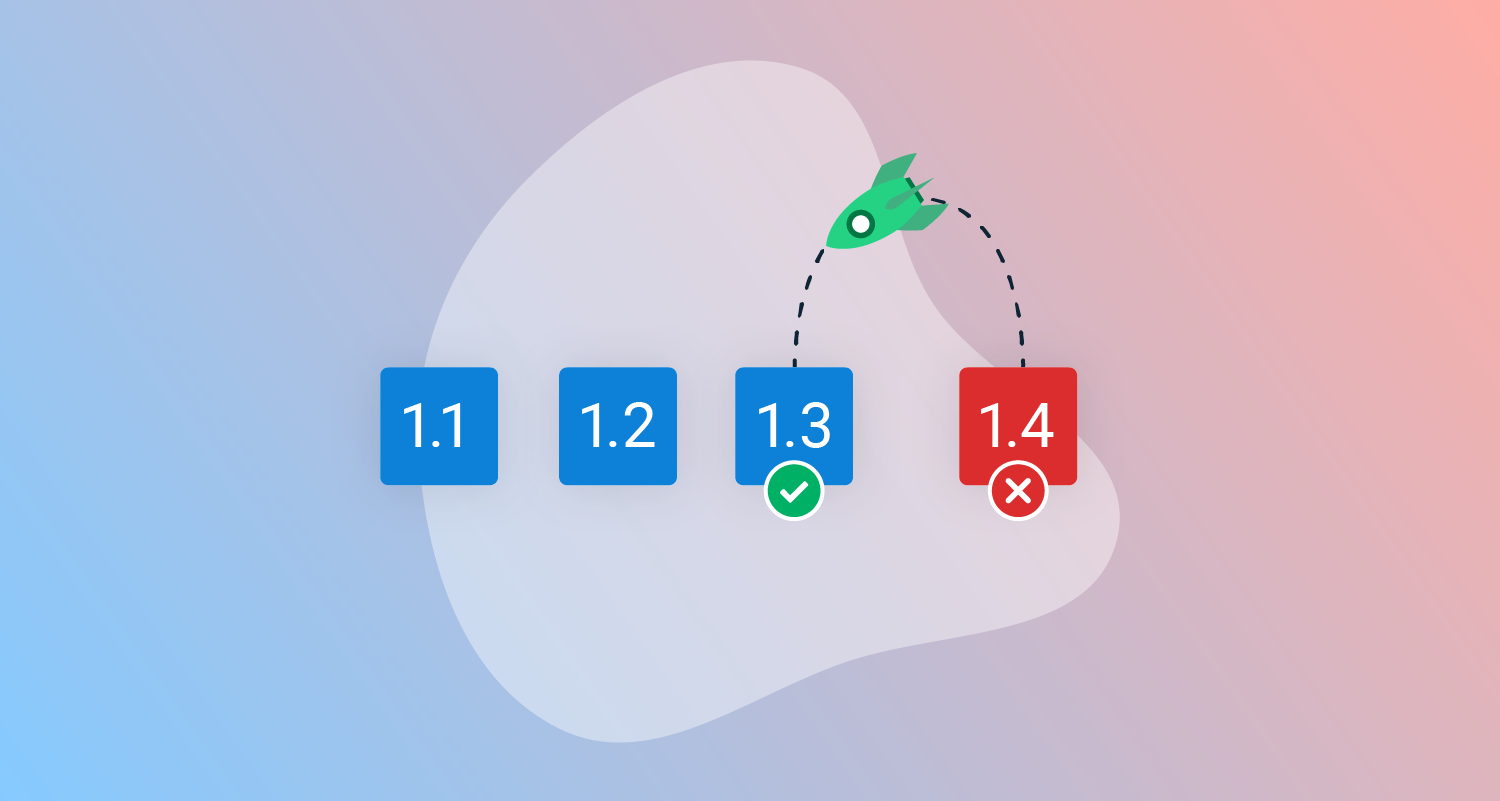
Modern rollback strategies
-

Benefits of isolated tenanted infrastructure
-
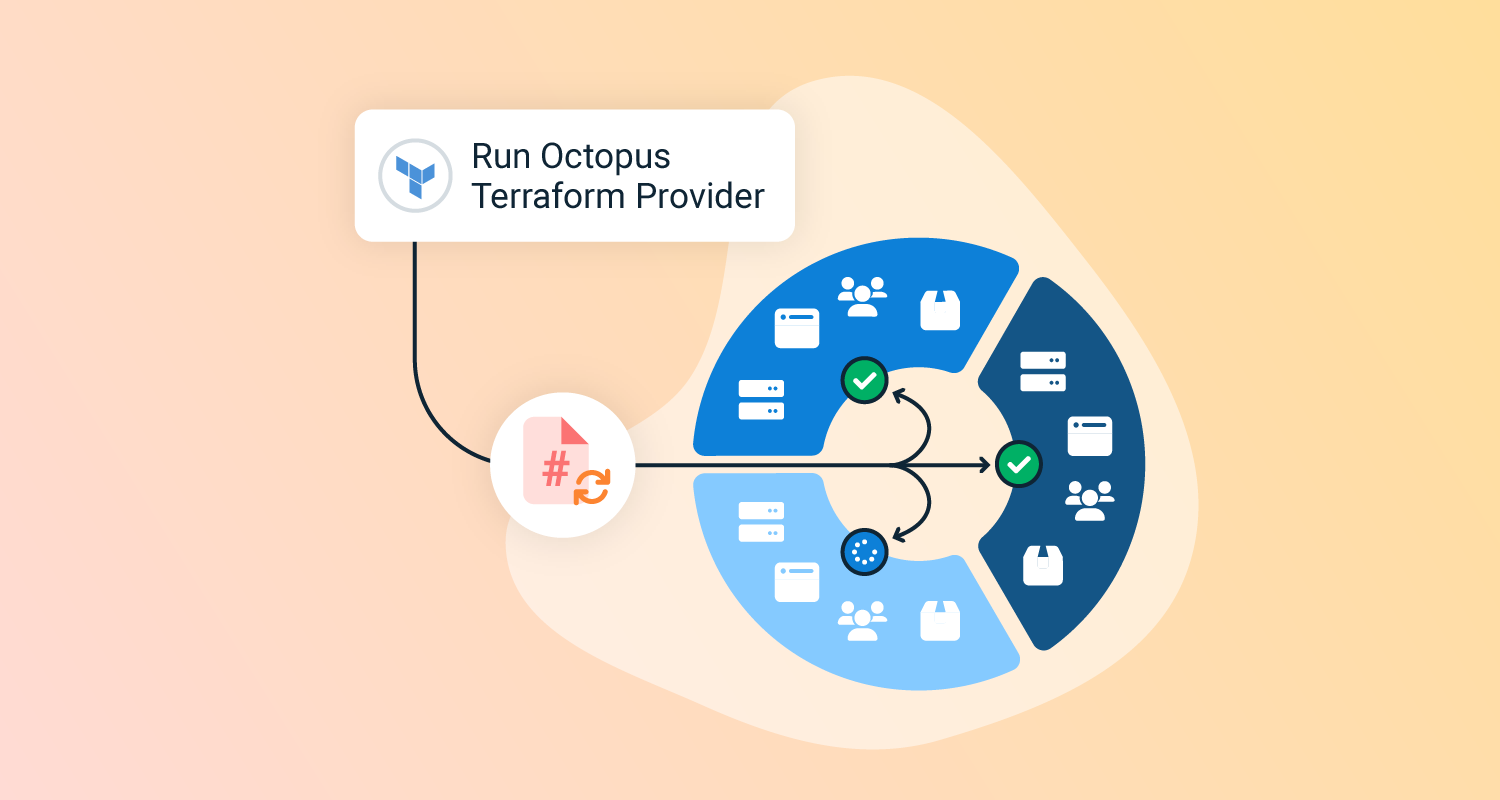
Using the Octopus Terraform Provider to create standards
-

Runbook lessons learned and recommendations
-

At the helm with Bob Walker
-
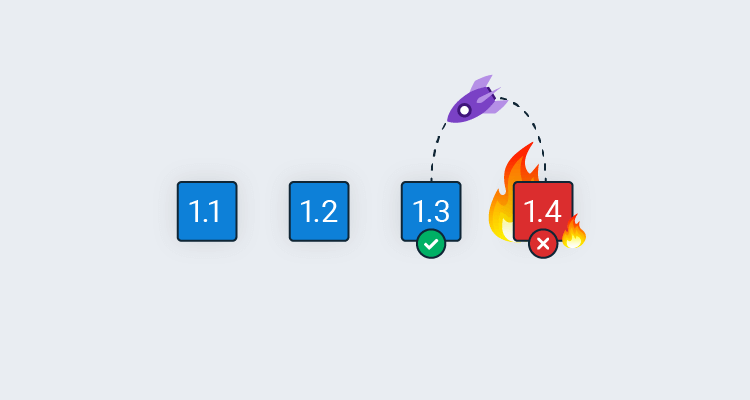
Rollback strategies with Octopus Deploy
-

Getting started with LDAP auth provider
-

Creating dynamic run conditions with new Octostache filters

Bob Walker (author) - Page 1
Related posts

Continuous Delivery Office Hours Ep.3: Branching strategies
Your branching strategy can support Continuous Delivery, or make it an impossible goal. We discuss the pros and cons of different approaches.

Proactive Dependency Security Best Practices
Learn how to proactively manage and secure your software from vulnerabilities and supply chain attacks.

Practical Platform Engineering in 5 Lunches: 5. Policies
Learn how to use policies to provide guardrails for projects to ensure they are compliant with organizational standards.


