-

Why you should track vulnerabilities after deployment
-

Cloud-native database deployment authentication
-

Continuous Delivery with Octopus and Kubernetes
-

At the helm with Kyle Jackson
-

What is cloud orchestration?
-
Using Docker as a package manager
-

Testing Kubernetes locally
-

What is a container registry? A guide + top 8 registries to consider
-
Maintaining your own version of the Azure CLI
-

Difference between docker.io, docker-cd, and Docker Desktop
-
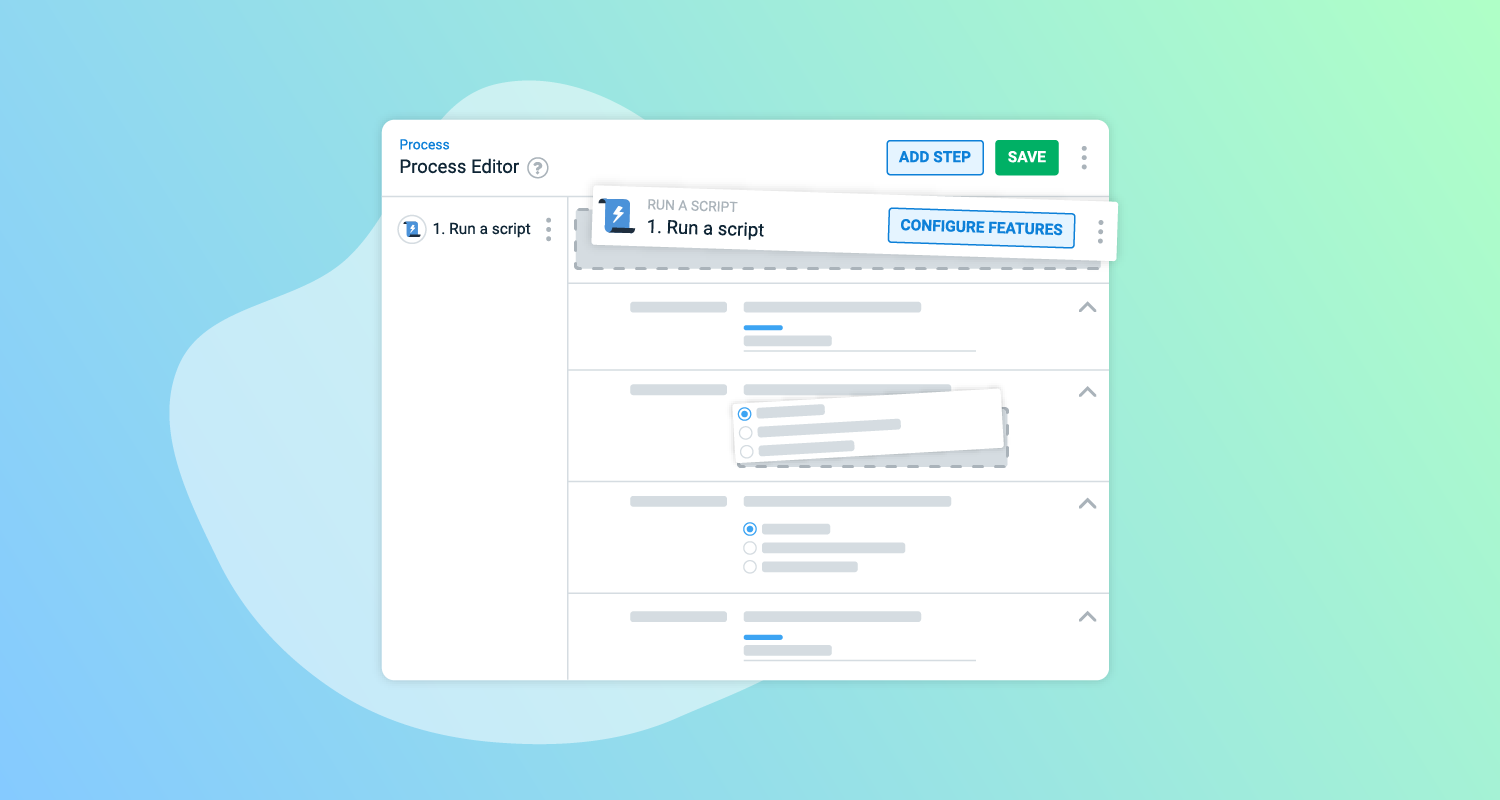
Improving delivery of your deployment steps
-

Configuring a GitHub NuGet registry as an external feed
Articles - Page 28
Related posts

Automatic superseded task cleanup
You can now configure Octopus to expedite deployment tasks by cancelling superseded ones.

Stop maintaining what your vendor now ships
Most practitioners have a custom solution running somewhere that a vendor has since solved in their product. The hard part is knowing when it's time to let it go.

GitOps with Octopus and Argo CD
Supercharge your Argo CD installation with Octopus in order to get the complete Continuous Delivery experience.








