What is release orchestration?
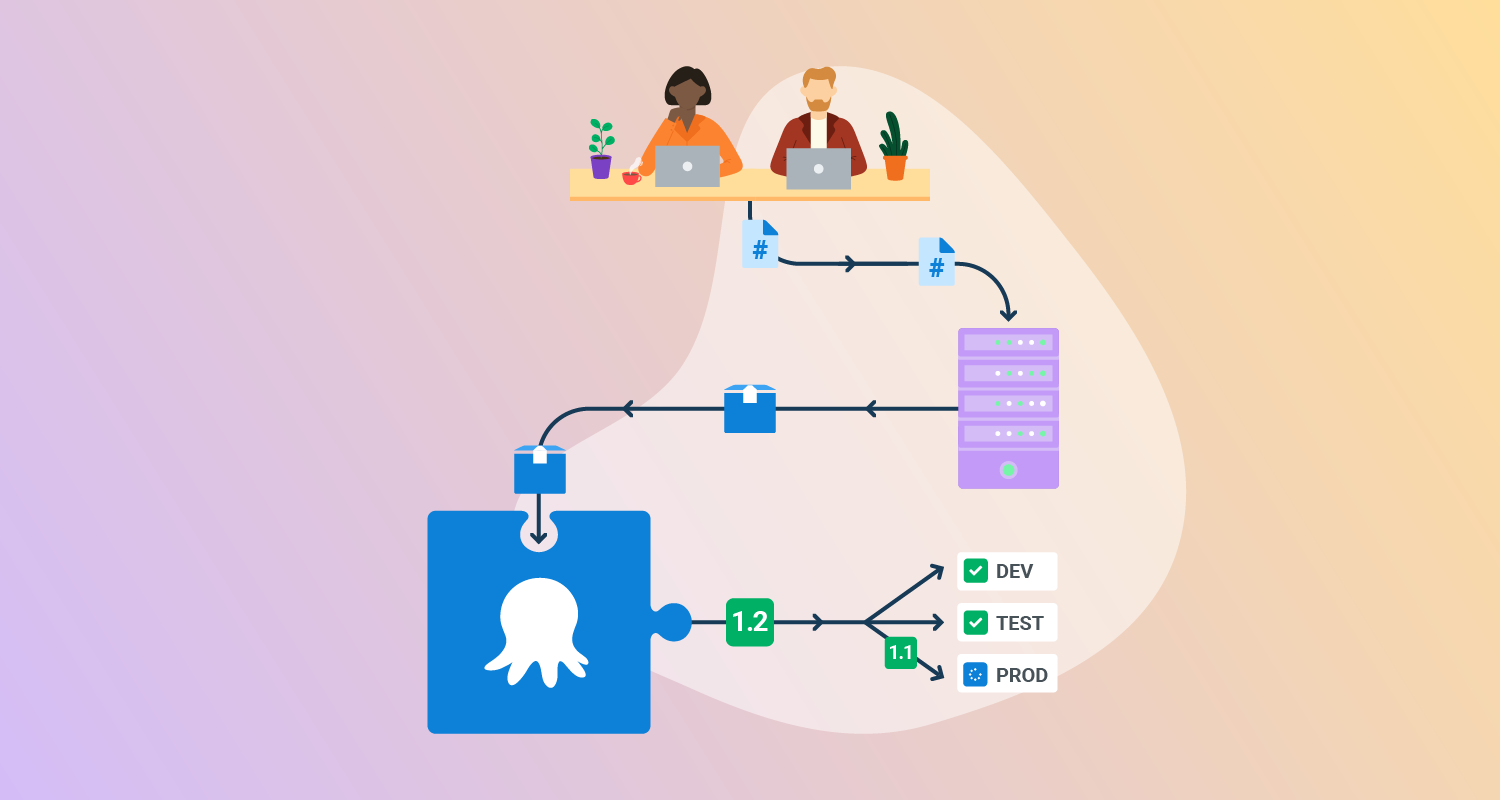
Release orchestration is the process of managing, coordinating, and automating the entire software release pipeline, from development to production. It is a crucial element of modern software delivery and DevOps, aiming to make releases more efficient, consistent, and less error-prone.
Release orchestration sits at the intersection of DevOps, automation, and Continuous Delivery. It addresses the complexities inherent in multi-team, multi-environment deployments. By connecting disparate tools and teams, it provides end-to-end visibility and control, making it possible to deliver updates and fixes quickly.
Key aspects of release orchestration include:
- Automation: Release orchestration uses automation tools to simplify repetitive and manual tasks, reducing errors and increasing efficiency.
- Coordination and integration: It connects various tools and systems in the release pipeline, such as version control, testing frameworks, and deployment tools, to ensure seamless workflows.
- Visibility and control: Release orchestration platforms provide a centralized view of the entire release process, enabling teams to monitor progress, identify bottlenecks, and make informed decisions.
- Governance and compliance: It helps organizations establish release governance frameworks, enforce compliance requirements, and maintain audit trails of changes and approvals.
- Collaboration: Release orchestration fosters collaboration and communication between development, operations, and other teams involved in the software delivery process.
This is part of a series of articles about software deployment.
Why application release orchestration matters
Application release orchestration aids in managing the growing complexity of software delivery. Modern applications often consist of multiple microservices, infrastructure configurations, and interdependent components.
Each release may require synchronizing updates across Kubernetes clusters, triggering schema migrations, coordinating with QA and SREs, and notifying downstream systems. Release orchestration platforms provide a structured, declarative approach to managing these workflows, replacing fragile ad-hoc scripts with reliable automation that scales.
As organizations aim to deploy faster and more frequently, the need for repeatability and consistency becomes more urgent. Application release orchestration ensures that teams can standardize processes across business units, reducing variability in how releases are executed. This standardization leads to fewer errors and more predictable outcomes.
How release orchestration works
Release orchestration implements an automated, end-to-end pipeline that guides software changes from development through deployment and validation in production. At its core it coordinates tasks, enforces sequencing and dependency rules, integrates with system APIs, and monitors outcomes to ensure reliable, repeatable delivery.
Typical workflow stages
In a typical orchestrated release pipeline, the following high-level stages occur:
- Trigger and intake: A change (commit, merge, or release trigger) kicks off the orchestration. The platform pulls the latest build artifacts, configuration definitions, and metadata from version control and artifact repositories to establish the release context. Scheduling policies (e.g., time-based or event-based) determine when pipelines run.
- Build and verification: Source code is compiled or build artifacts are produced. Orchestration invokes automated testing layers (unit, integration, functional tests) in defined order, collecting results and gating progress on pass/fail criteria. Early validation helps ensure only high-quality artifacts move forward.
- Environment preparation: Environments (dev/test/staging/prod) are provisioned or configured using infrastructure definitions (e.g., declarative manifests). Orchestration may call out to Infrastructure as Code systems to ensure target environments match expectations (e.g., network, storage, service dependencies).
- Deployment sequencing: Releases are deployed according to strategy (e.g., blue-green, canary, rolling update). Orchestration controls the order of operations and ensures that prerequisites (schema migrations, feature toggles) are executed in the correct sequence with appropriate checks between steps.
- Approval and policy enforcement: Business or compliance policies may require manual reviews or automated policy checks before advancing. Orchestration bridges automated tasks and any required approvals to maintain governance without breaking automation flows.
- Post-deployment validation and monitoring: Once changes land in production, orchestration connects to observability systems to verify stability, run smoke tests, and evaluate metrics. If anomalies are detected, automated rollback or mitigation steps can be triggered.
- Feedback and reporting: Throughout the pipeline, orchestration emits logs, status updates, and dashboards to provide visibility into the release state. This continuous feedback loop supports rapid debugging and informed decisions.
Key technical approaches
Release orchestration can be implemented using several general approaches, which define how the coordination logic is expressed and executed:
- Workflow orchestration engines: Declarative pipelines define sequences of tasks and conditional logic (e.g., pipeline as code). The orchestration engine interprets these workflows and schedules tasks accordingly. This approach supports complex branching, retries, and rollbacks.
- Event-driven coordination: Orchestration reacts to events (e.g., test success, environment ready) using event brokers or messaging mechanisms. This ensures that downstream stages only run when upstream conditions are satisfied, enabling loosely coupled components to work together.
- Model-based orchestration: High-level models (e.g., release definition manifests, state machines) describe desired states and dependencies. The orchestrator continuously reconciles the actual state with the desired state, making adjustments and triggering actions until alignment is reached.
- Pipeline as code patterns: Declarative configuration files represent release logic in human-readable form. This allows versioning of orchestration logic, reusability of templates across environments, and easier audits of what actions will occur in a release.
Integration and control mechanisms
Across these stages and approaches, release orchestration typically integrates with common DevOps interfaces:
- Version control APIs to detect changes and fetch code/version metadata.
- Build and test systems to launch and monitor automated verification jobs.
- Environment provisioning frameworks (containers, Kubernetes manifests, or VM orchestrators) to prepare target infrastructure.
- Monitoring/observability platforms for post-deploy validation and performance checks.
- Approval systems and policy engines for governance and compliance gates.
These integrations work together so that the release process is not a set of isolated scripts but a cohesive, observable, and controllable pipeline that can adapt to complex dependencies and organizational policies.
Key aspects of release orchestration
Automation
Automation in release orchestration eliminates manual intervention across repetitive, error-prone tasks such as deployments, test executions, environment setups, and rollback operations. This is typically achieved through declarative pipeline definitions or workflow templates that specify exact steps, conditions, and expected outcomes.
Automation supports parallelization of tasks (e.g., deploying to multiple environments simultaneously), conditional execution (e.g., only run integration tests if unit tests pass), and dynamic workflows (e.g., retry on failure with exponential backoff). It also enables integration with secrets management systems to securely inject runtime credentials or tokens.
Visibility and control
Release orchestration platforms provide comprehensive visibility into the execution of release pipelines. This includes real-time dashboards that show pipeline status, stage durations, success/failure outcomes, and historical trends. Logs from each task are captured and surfaced for debugging, while metrics such as deployment frequency, lead time, and failure rate help teams evaluate performance.
Control mechanisms include manual gates, pause/resume features, and conditional branching logic. For example, a deployment to production can be paused pending sign-off, or a pipeline can be configured to skip certain stages in a dry-run scenario.
Governance and compliance
Release orchestration helps enforce governance policies that are critical in regulated or security-conscious environments. This includes enforcing stage-level approvals (e.g., from security, QA, or management), requiring successful completion of compliance checks (e.g., vulnerability scans, license audits), and maintaining immutable audit logs for every action in the pipeline.
For example, a pipeline can require approval from a compliance officer before deploying to production, verify that security scans have passed with zero critical findings, and log all actions with user IDs and timestamps. These logs can be exported for compliance reporting or integrated with systems like ServiceNow or Jira for change tracking.
By embedding compliance into the release process, organizations can maintain velocity while still meeting internal and external regulatory requirements (e.g., SOC 2, HIPAA, ISO 27001).
Collaboration
Effective release orchestration fosters collaboration across development, operations, QA, security, and business stakeholders. It does this by exposing a shared, transparent pipeline where all participants can see what is happening, what has completed, and what is pending.
Role-based access control ensures that each team can contribute to the process without overstepping boundaries—developers push code, QA reviews test results, ops oversee deployments, and security signs off on scans. Built-in notifications (e.g., Slack, email, Teams) inform the right people at the right time—whether that’s a test failure alert or a request for deployment approval.
Orchestration also reduces reliance on tribal knowledge or one-off scripts, making release processes more maintainable and understandable by anyone on the team. When issues arise, shared logs and metrics allow teams to troubleshoot collaboratively, shortening time to resolution.
Benefits of release orchestration
A well-implemented release orchestration strategy delivers measurable value across engineering, operations, and compliance. Below are the key benefits organizations gain from adopting release orchestration:
- Accelerated release cycles: Automated workflows and coordinated processes allow teams to release software faster, moving from code commit to production in hours instead of days or weeks.
- Increased reliability and consistency: Standardized pipelines reduce variability between deployments, minimizing human error and ensuring consistent execution across environments.
- Improved visibility and traceability: Centralized dashboards, audit logs, and real-time monitoring provide full transparency into release progress, enabling quick diagnostics and historical analysis.
- Better risk management: Built-in approval gates, rollback mechanisms, and testing checkpoints reduce the risk of introducing defects or non-compliant changes into production.
- Enhanced collaboration across teams: Shared tools and communication channels align development, QA, security, and operations, reducing miscommunication and delays.
- Scalability across projects and teams: Reusable workflows and templates make it easier to manage releases across multiple applications, teams, and regions without reinventing processes.
- Simplified compliance and auditing: Automated enforcement of policies and capture of change records simplify reporting and help meet internal and external regulatory requirements.
Challenges of release orchestration
While release orchestration is critical for complex software projects, it can raise significant challenges for organizations.
Manual drift
Manual drift occurs when teams make changes to environments or processes outside the orchestrated pipeline, leading to inconsistencies and unpredictable release outcomes. For example, an engineer might apply a quick fix manually in production to address a pressing issue but not document the change in the source pipeline.
These undocumented changes accumulate, creating discrepancies between what is tested, staged, and run in production. Such drift undermines the benefits of release orchestration, introducing new sources of failure and complicating audits and rollbacks. Unmanaged manual interventions break the repeatability and reliability that orchestration aims to enforce.
Tool sprawl
Tool sprawl refers to the proliferation of disparate, disconnected release tools across an organization. Development, QA, operations, and security teams might each select different solutions for automation, monitoring, or deployment, resulting in bloated toolchains and minimal standardization.
This fragmentation complicates integration, increases maintenance overhead, and often leaves teams struggling with knowledge gaps or inconsistent workflows. Managing tool sprawl requires deliberate architectural choices and governance.
Over-engineering complexity
Over-engineering appears when organizations introduce unnecessary complexity in their release orchestration processes—often through excessive scripting, custom workflows, or non-standard integrations.
This complexity can hinder onboarding, slow down releases, and make troubleshooting problematic. As the orchestration landscape grows, so does the likelihood of fragile pipelines and hidden dependencies that are hard to maintain and upgrade.
Best practices for reliable release orchestration
Organizations should consider the following practices to help plan their release orchestration strategy.
1. Standardize environments and processes
Standardizing environments is critical for repeatable, predictable releases. Using Infrastructure as Code and configuration management tools, organizations can ensure all development, test, and production environments are consistent. This eliminates a major source of deployment failures caused by mismatched libraries, misconfigured resources, or undocumented manual changes.
Process standardization is equally important. Clearly defined release procedures, automated checklists, and playbooks make operations scalable and auditable. By embedding best practices into the orchestration toolchain, teams can rapidly onboard new members, execute releases confidently, and continuously improve delivery based on historical feedback.
2. Automate compliance checks early
Automating compliance checks at the earliest stages of the release pipeline prevents costly rework and production risks. Embedding security scans, code quality analysis, and policy enforcement from the initial commit phase ensures that only compliant and secure code advances. Automation catches violations at the source, making remediation faster and preventing bottlenecks during critical release windows.
These early checks should cover regulatory standards relevant to the organization’s industry, such as GDPR, HIPAA, or PCI DSS. When compliance automation is integrated with orchestration, artifacts, logs, and audit trails are generated automatically, simplifying later reviews and audits.
3. Use progressive delivery for risk mitigation
Progressive delivery techniques—such as canary releases, blue-green deployments, and feature flagging—reduce the impact of failed deployments. By gradually rolling out changes to small subsets of users or infrastructure, organizations can monitor real-world performance and catch issues before a full production rollout. Release orchestration platforms often automate this gradual approach and include real-time metrics for decision-making.
Incorporating progressive delivery at the orchestration level allows for fail-safe mechanisms like instant rollbacks or pausing rollouts if errors exceed a threshold. This not only supports rapid innovation but also protects customers and business systems from widespread outages.
4. Pipeline as code
Pipeline as code involves defining release workflows in machine-readable formats like YAML or JSON, stored in source control. This practice brings all the benefits of code versioning, peer reviews, modularity, and rollback to release management. Changes to the pipeline itself are transparent, auditable, and subjected to rigorous change control processes, ensuring consistency over time.
With pipeline as code, teams can rapidly validate and iterate on release workflows. It enables collaboration across distributed teams, reduces onboarding time for new team members, and provides a living documentation of the release process. Over time, it simplifies maintenance and supports more advanced use-cases like dynamic branching, parameterization, and cross-project template reuse.
5. Metric-driven automation
Metric-driven automation uses real-time data to drive release decisions, such as advancing, pausing, or rolling back a deployment automatically based on key indicators. Metrics—like error rates, performance baselines, or business KPIs—can be integrated directly into the orchestration workflow. This makes releases safer, as the system reacts faster than manual oversight to regressions or anomalies.
By placing metrics at the core of release orchestration, organizations move closer to self-healing systems. Automated gates, alerts, and conditional logic empower teams to experiment confidently, knowing that objective data—not subjective guesswork—governs the flow of production changes.
Help us continuously improve
Please let us know if you have any feedback about this page.